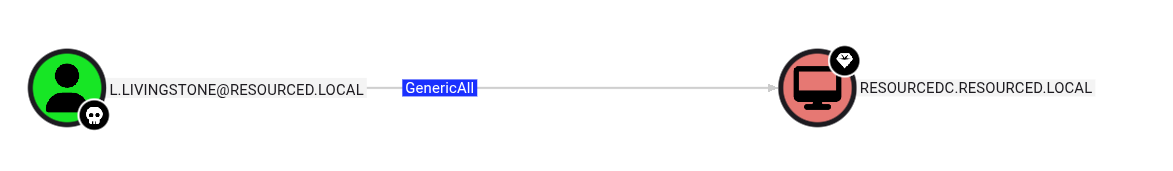
GenericAll permission on a domain computer
GenericAll permission on a domain computer
The user l.livingstone has GenericAll permission on the domain computer RESOURCEDC$.
GenericAll grants full control over the object — including the ability to write to msDS-AllowedToActOnBehalfOfOtherIdentity. This makes Resource-Based Constrained Delegation (RBCD) abuse possible: we create a machine account we control, configure the target to trust it for delegation, then impersonate any user (including Administrator) to obtain a service ticket via S4U2Proxy.
Step 1 — Add a fake computer to the domain
impacket-addcomputer creates a new machine account in the domain. We authenticate as l.livingstone using her NTLM hash.
Step 2 — Configure RBCD on the target computer
Using our GenericAll rights, write fake$ into the msDS-AllowedToActOnBehalfOfOtherIdentity attribute of RESOURCEDC$. This tells the target to trust fake$ for delegation.
Step 3 — Request a service ticket as Administrator
Using impacket-getST, perform S4U2Self + S4U2Proxy as fake$ to obtain a CIFS ticket impersonating Administrator.
Step 4 — Export the ticket
Set the KRB5CCNAME environment variable so Impacket tools pick up the saved ticket automatically.
Step 5 — Connect via psexec
Since we authenticate with Kerberos, the target’s hostname must resolve correctly. Add an entry to /etc/hosts if needed, then connect using the ticket.